A guide to Data Bearing Devices/Assets. Download your free copy here >
30 common places your company data is stored (and waiting for a breach)
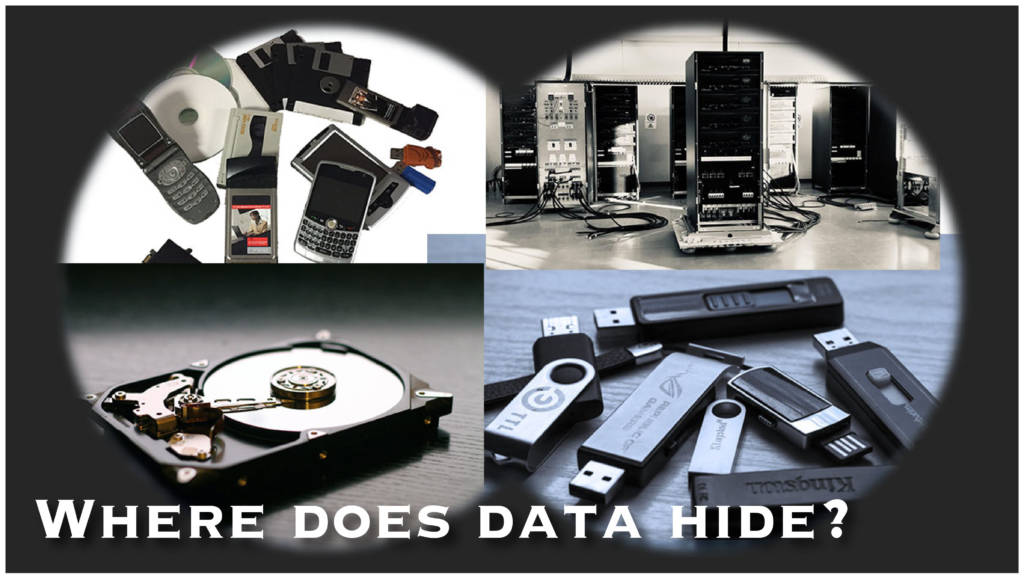
Data destruction is the last phase of IT equipment lifecycle planning. The end goal is to make sure that no data remains on lease returns, equipment bound for recycling or handed over to the next guy in line for a replacement laptop. Knowing where your data is stored (or hiding) is an essential part of preventing a data breach.
It’s not a scavenger hunt
But it can feel like it. IT equipment is super complex these days (and it’s getting smarter every day). Knowing where to find the data so that you can make a comprehensive plan for data destruction is getting harder and harder.
30 places your company data may be stored
Here’s a quick list of common and possibly overlooked corporate devices and office equipment that are storing (hiding?) your data. Any one of them could be a huge risk for a data breach.
- Work-issued laptops and desktop computers
- Personal/home computers
- Motherboards with SSD drives
- Thumb drives / USB drives
- External hard drives
- Tablets
- Badges, IDs
- X-rays
- CDs and DVDs
- Copiers
- Printers
- Hard drives
- Solid State Drives (SSD)
- Cell phones
- Point of Sale (POS) Devices
- Tapes/Magnetic tapes
- Arrays
- Storage area networks (SAN)
- Network area storage (NAS)
- Backup tapes / magnetic tapes
- JAZ and ZIP discs
- Memory chips and sticks
- Military gear
- Smart phones
- Video tape
- Transmitters
- Pagers
- Rental cars and lease returns (smart phone connection)
- Shipping/inventory scanners
- Cloud service providers (data centers and their backups)
Help is right here
Your ITAD, VAR or even head of data security should be able to help you put together a list of possible sources that could be holding onto potentially harmful company data. And advise you on a best practices plan to ensure that the data is destroyed so that you can rest easy.
If you need help, talk to us. Without obligation. We’re happy to give you a quick evaluation of data destruction options so that you can stomp out risk wherever it may be. And, we can refer you to a VAR or ITAD if you need one.
To learn more about data destruction options, download our Data Destruction 101 guide or read our data destruction services section of the website. And, if we missed a data hidey-hole that you’ve discovered, let us know.