The unrelenting hunt for DBDs as part of the IT asset disposition process is a critical first step in data security and compliance
How can you ensure data destruction compliance when data bearing device (DBD) and data bearing asset (DBA) identification is hit or miss, misunderstood or not prioritized within your organization? Making disposition even more complex, different departments and locations may have different (and conflicting) approaches to data storage management.
Sharing our expertise underscores the importance of having an internal team or an external resource dedicated to safeguarding your company’s data. Guardian’s DBD detectives, in actuality highly trained IT technicians, specialize in locating and identifying common and obscure data storage across all types of IT devices and office equipment.
Why it’s so difficult to find data bearing devices
There two general situations that add complexity to the search for undetected and concealed DBDs and DBAs:
- Manufacturers change equipment designs constantly. In addition, their OEM (original equipment manufacturer) suppliers may also change their component hardware design. These changes may or may not be documented or available.
How to reduce risk: Assume nothing is ever the same as the last time or as documented. Do not rely on manufacturer documentation (if it’s even available) to determine if there’s an embedded SSD on a motherboard installed below a fan or a separate micro SSD that was added to improve processing speed. Or something else.
- Once it’s in your facility, installed IT equipment is modified, expanded, repaired or replaced all the time. The “upgrade” or fix may be done on the fly or planned but it’s unlikely that any added memory, drive or card pulled from your inventory is documented when it’s installed.
How to reduce risk: Assume IT asset modifications were made to either optimize performance or prevent a problem but with zero consideration to the impact on EOL data compliance.

Where to find data bearing assets and devices
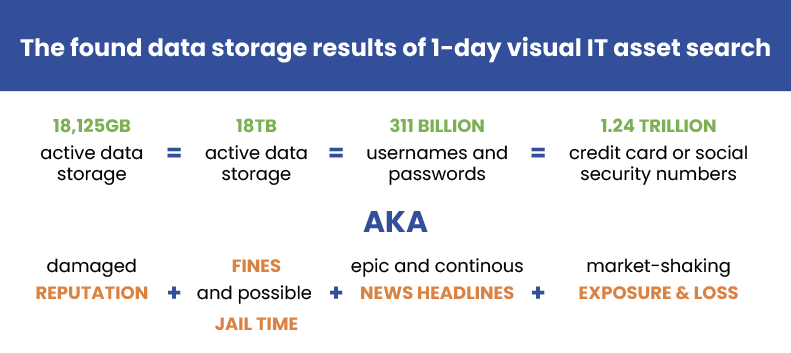
It’s virtually impossible to provide a complete reference document that lists where you’ll discover a data bearing device or asset. There are hundreds of variations based on the hardware brand and type that your offices, facilities, data centers and employees use (purchased and leased) and access. And DBDs and DBAs are added everywhere to all types of IT equipment: bottom, sides, front, back, below and onboard – places only a trained tech would even know to look at and in a myriad of recognized data storage form factors.
A few examples of DBDs and DBDs that the Guardian Data Destruction team found as a result of a physical, visual search (and missed in the customers’ searches): All unknown, undocumented and a surprise!
- SDs, SSDs, tiny HDDs, ATAs in firewalls (Cisco, Fortinet)
- VPDs, HDDs, PCIe SD card, NVMEs and microSDHCs buried deep in servers (IBM, Dell, Cisco, etc.)
- SDs, HDD and SSDs in server chassis
- mSATAs, PATA, PCIes in Arista, Cisco, IBM, Juniper switches
- Plug-in USBs and SATA//NVMe expanded memory expansions in Nutanix and Pulse Tech servers
- HDDs and SDs in printers and copiers (Toshiba, Canon, HP, Konica-Minolta, etc.)
- SDs, SATADOMs and SSDs inside all kinds of rack-mounted server equipment including infrastructure managers, fiber interconnects, secure remote access modules, voice logging modules, etc.
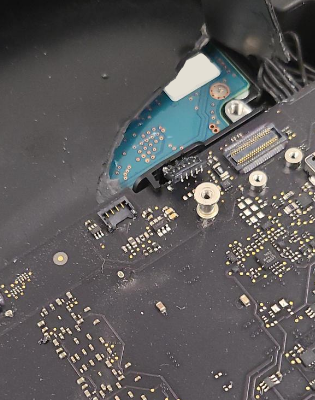
- SSDs sealed inside of laptop equipment including Apple Minis, Microsoft Surfaces and other thin client technologies
In each case, the DBD or DBA was undocumented, unrecognized and completely overlooked on outbound IT equipment. Without deep knowledge and a thorough, physical search by a trained team, the data held by these real life occurrences would have been undetected and released outside the organization. Use these examples to shine a light on possibilities within your own organization. (Or, talk to Guardian about improving your operation to include this final IT check.)
Guardian’s DBD-discovery guidelines
The process of locating DBDs is a mix of knowledge, experience and ninja; we build on what we’ve learned and roll-in new information as it is revealed. We say, “Curiosity is your weapon.”
- Data is always more valuable than the hardware.
- Assume nothing.
- Disregard the premise of model number consistency. Check all assets even if they are the same model and year.
- Disregard age because old IT hardware can be as sneaky as new IT equipment. Note that older IT assets are more likely to use larger form factors which may be easier to spot.
- Have the mindset that each device is holding a secret and it is your mission to uncover it.
- Do not rely on software tools as a method of location and verification as they do not recognize or indicate data storage that is seated improperly, unplugged in or defective, infected or corrupt.
- Even if one or more server blades do not have SSD add-on cards, you must still check every single one (often we find just one non-standard item in a batch of no-risk, vanilla IT assets).
- Do not rely on the presence of quick-release levers to identify a hard drive from the front of a server.
- If the asset has video output, it has data input and likely has some type of data storage.
- Do not rely on procurement or other documentation for tracking individual assets.
- Look for the uncommon. Paradoxically, distrust the common.
- Unscrew or open panels to look deeper.
- If it looks suspicious, be relentless.
- Be aware of dumb devices (they are getting smarter).
- Leased equipment gets the same scrutiny as owned equipment.
- Always be safe with tools when exploring. Be especially respectful of lithium ion batteries.


Guardian’s best practices for DBD documentation and education
- Document every case.
- Include photo documentation of the asset, specific details of where the data risk was found and what type of data storage was located.
- Always photograph and record the serial number of found DBDs.
- Share all nw discoveries quickly with your immediate team.
- Ensure that stakeholder permissions and awareness are up to date.
- Develop a process that continually educates your team, stakeholders and third-party vendors.
- Develop a hit (or hot) list of IT devices or brands that consistently have added data storage.
- Develop regular and consistent reporting methods.
- Create a pictorial reference guide
Proper lifecycle disposition of data bearing devices
In addition to a meticulous process for identifying data bearing devices and determining their disposition, it is crucial to understand your organization’s compliance needs and risk factors to effectively implement all data destruction processes. If you need help, talk to a Guardian. Working through your ITAD, VAR, MSP or IT resellers, we can help develop a comprehensive process for identifying and removing data bearing devices and applying the most appropriate NIST Standard data sanitization process.
Guardian Data Destruction partners with ITADs, VARs, MSPs and IT resellers to support their customers who demand a gold standard of data compliance and destruction. We provide best practices in data destruction (shredding, erasure, degaussing), white glove IT asset packing and secure logistics or enterprise and data center services.
Read next
- Get our list of data bearing devices and data bearing assets >
- Perception vs reality in the physical search for DBD (a guide) >
- Browse Guardian Data Destruction’s services (available through ITADs, VARs, MSPs) >
- How data walks out facilities on unknown, undocumented data storage >
Sign up for email updates to receive the latest in data security options from Guardian Data Destruction >