A guide to Data Bearing Devices/Assets. Download your free copy here >
What is a Certificate of Data Destruction?

Perhaps you’ve been asked to provide a certificate of data destruction due to an audit or routine chain of custody verification. Or worse, the fallout from a data breach.
Ensure that your data destruction process is airtight by understanding what the certificate of data destruction is and the verification you’ll need for an effective, compliant data destruction plan that stands up to scrutiny.
And, lets you sleep at night.

What is a Certificate of Data Destruction?
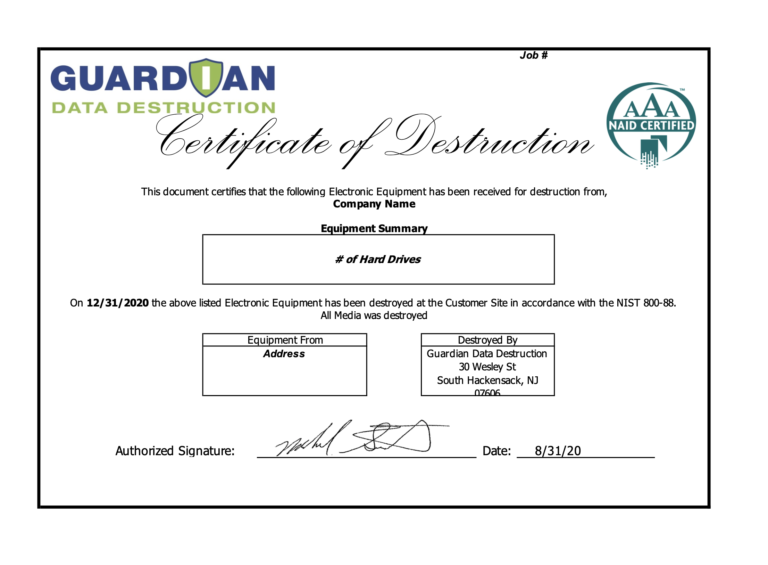
Quite simply, a Certificate of Data Destruction is a formal document stating that digital media has been destroyed.
It should include detailed information about the method of destruction, a detailed list of IT devices (hard drives, SSD drives, magnetic tape, cell phones, USB drives, arrays, etc.) destroyed to ensure that the data destruction process complied with all relevant security laws, most importantly NIST 800-88 specifications.
Are all Certificates of Data Destruction the same?
There is no certifying authority for the data destruction industry so the reputation, reporting capability and legitimacy of your data destruction vendor is paramount.
In other words, choose carefully.
ITADs, VARs, IT resellers and MSPs, if you’re using a data destruction partner, they should automatically provide ample verification that will protect you, your client, and your client relationship in the unfortunate circumstance of either legal action, a data breach investigation, or an audit of your data destruction process. Without the verification, the Certificate of Data Destruction doesn’t provide absolute proof of data privacy regulatory compliance and best practices.
For businesses going direct to a data sanitization provider, ensure that you are using a service that provides the chain of custody, serial number tracking, verified software when erasing (wiping) and other verifications that ensure that their Certificate of Data Destruction holds weight if you are challenged.
How to find the best data destruction provider
We’ve put together a handy How to select a gold-standard data destruction provider checklist of criteria that your data destruction provider should have or provide to support a strong Certificate of Data Destruction.
Your ITAD, VAR or even head of data security should work with you to develop the right criteria for selecting the right data destruction vendor to meet your standard. And advise you on a best practices plan to ensure that the data is destroyed so that you can rest easy.
Guardian can help with a data destruction solution
If you need help or are concerned about your current data destruction process (and the value of your Certificate of Data Destruction), talk to us. Without obligation. Our experts will answer any questions to ensure that your IT assets are certified (really certified) to be data free. And, because we don’t go direct, we will refer you to a VAR or ITAD if you need one.
Read next
- Answers to your FAQ hard drive shredding questions
- All about data destruction services
- Download our (free) NIST vs DOD data destruction guide
- How to choose a data destruction process
Sign up for email updates to receive the latest in data security options from Guardian Data Destruction >