A guide to Data Bearing Devices/Assets. Download your free copy here >
Asset Checklist for your IT Risk Management Plan

IT risk management strategies are focused on security breach prevention. That’s a big mandate. In addition to hacking and cybercrime prevention, information technology departments need to know which assets are collecting, holding, creating and sharing secure and private information.
IoT, auto-backups, outside vendors, advanced technology and smaller chip sizes have made everyday objects smart and expanded the capacity and capability of computerized devices. These advances streamline processes and make us more efficient. And better decision-makers.
That’s cool.
Until the device’s data is no longer secure and becomes an opportunity for a breach.
Aaaand…..that’s not so cool.
The information risk typically stems from a lack of awareness and processes about end-of-life, end of contract, end of vendor relationships, technology migrations, worldwide pandemics, a remote workforce and the unsecured shipping of devices with live data.
IT risk management hinges on identifying and analyzing all data storage devices
Data is no longer on just laptops, desktops, servers and the cloud. It’s everywhere. Offices, data centers, field equipment and devices hold confidential data that may be “found” by an unauthorized user during any stage of recycling, refurbishment, repair, remarketing, storage, shipping, resale or on a loading dock or closet waiting for processing.
The gap in asset knowledge and tracking can lead to a data breach, legal inquiry, fines and a TKO to your brand.
All because someone didn’t know a hard drive was “there”. Whoops.
An Asset Checklist to Evaluate for IT Risk Management
Equipment, devices and situations that may be storing data and creating vulnerabilities in your IT risk management plan.
Who is this guide for? Information technology departments including IT asset managers (ITAM) and IT security, procurement, engineers, legal teams, ITADS, office managers and facilities managers who know what equipment, machines and devices are in the office, the factory, the workforce and the home.
Importance of this guide: Use our checklist to learn just where data may be stored. Incorporate findings into your overall risk prevention program and enlist other departments to help you shut the risk down. Review your data destruction programs and protocols and embed them in your IT process.
The Obvious
- Computers – laptops, desktops, tablets, Chromebooks, MacBooks, all-in-ones
- Network equipment – routers, switches, firewalls, NAS, transmitters/transceivers with chips
- Data Servers/Storage – arrays of hard drives and tape backup systems
The Forgotten
- Add-on and replacement hard drives – not original to the PO or spec
- Backups of the backups – your cloud partners/storage facilities/Internet provider
- Old/unused accounts – email, YouTube, Dropbox, etc.
- Computer and virtual trashcans emptied – even your cloud? (Most are auto-set to empty after 30 days. Or never.)
The Hiding in Plain Sight
- Magnetic strips – credit cards, security badges and IDs
- Office equipment – copiers, printers, scanners (HDD or SSD or both)
- Cameras, video cameras – MicroSDs, tapes
- External storage – thumb/USB drives/sticks, tape drives and libraries, JAZ/ZIP/hard drives, CDs and DVDs, videos
The Surprises
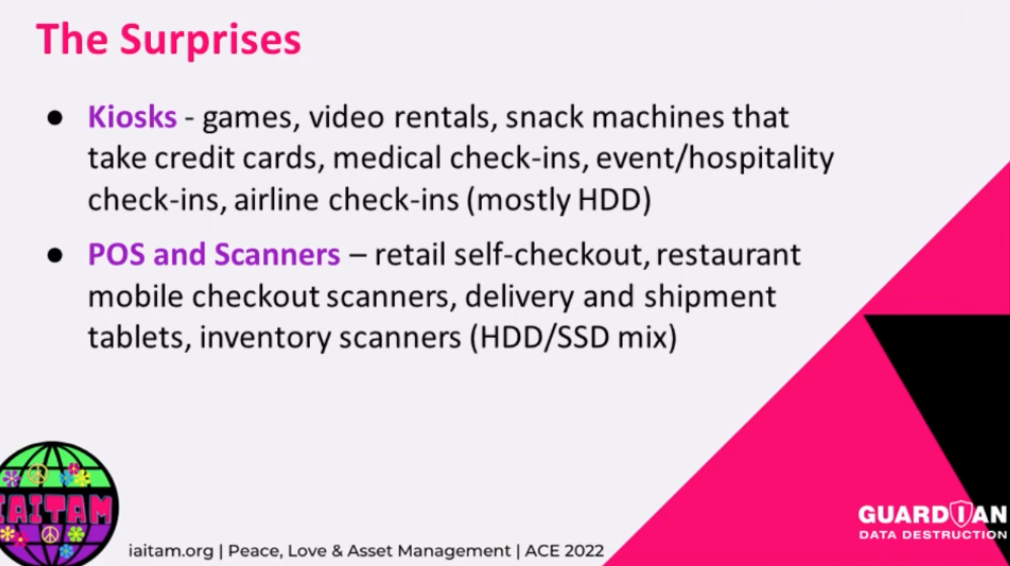
- Kiosks – games, video rentals, snack machines that take credit cards, medical check-ins, event/hospitality check-ins, airline check-ins (mostly HDD)
- POS and Scanners – retail self-checkout, restaurant mobile checkout scanners, delivery and shipment tablets, inventory scanners (HDD/SSD mix)
The Innocuous
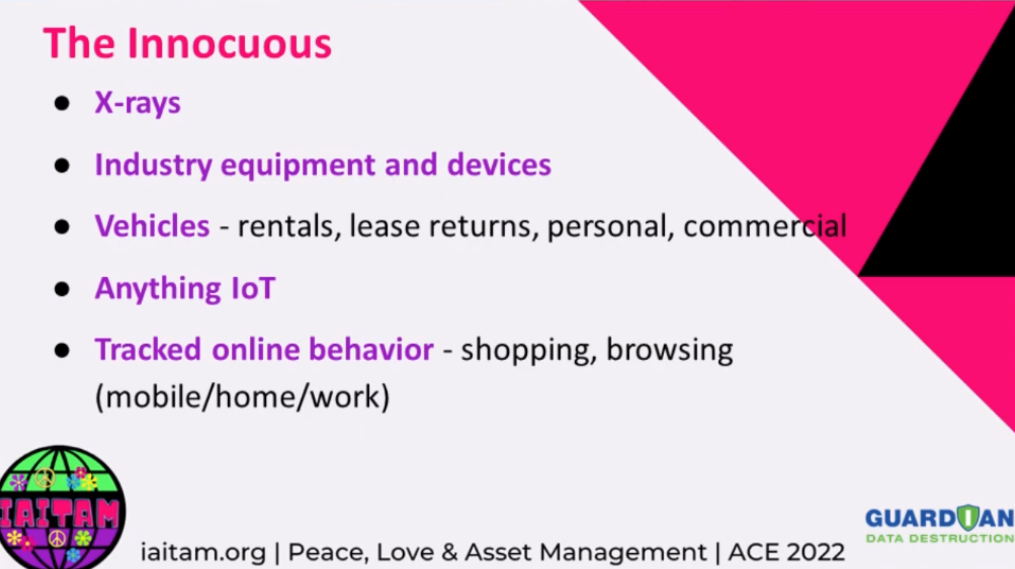
- X-rays
- Industry equipment and devices
- Vehicles – rentals, lease returns, personal, commercial, cars, trucks
- Anything IoT
- Tracked online behavior – shopping, browsing (mobile/home/work)
- Unauthorized software
The Super Sneaky
Instead of thinking about the device or asset, let’s reverse our thinking. Start with the memory technology. Then look for the technology inside your devices and assets.
Ex 1: SSDs
- They’re everywhere because they’re small
- They can hold a lot of confidential documents in almost no space
- “What devices/equipment do I have that have SSD drives?”
- Copiers, printers, scanners, any media, motherboards (standard), etc.
- Memory cards – chips M.2 SSD – servers, desktop
- MicroSD cards – cameras, printers, drones
- More
Ex 2: Servers
Memory configurations are not standardized so every single one could be unique (we’ve seen it) and memory is often not documented as servers are upgraded or expanded after original purchase. Look for these common setups:
- Standard, no-surprise hard drives – all in one place as listed (what you’d expect)
- Hard drives located in multiple places on a single server – front/rear/legacy
- External hard drives + internal hard drives + one or more SSDs on the motherboard
- OS system on a MicroSD accessed through the controller
- Hundreds more….
Ex 3: IT Provisioning
Thanks to the pandemic and the expanded remote workforce, more and more IT departments rely on auto-device enrollment, provisioning and deployment processes (called MDM for Mobile Device Management) to increase enterprise security and decrease manual IT management.
When it comes to data destruction, you must have a process to un-enroll devices from your IT provisioning process.
Unawareness of MDM setup and removal can eliminate any possibility of redeployment, resale, donation and data destruction. If you’re unaware of MDM-enrollment, devices will auto-reprovision with initial setup data, access, software and your company identification even after the HD/SSD is erased and shredded. (Hello data breach and brand trouble.)
The Takeaway for IT Risk Management
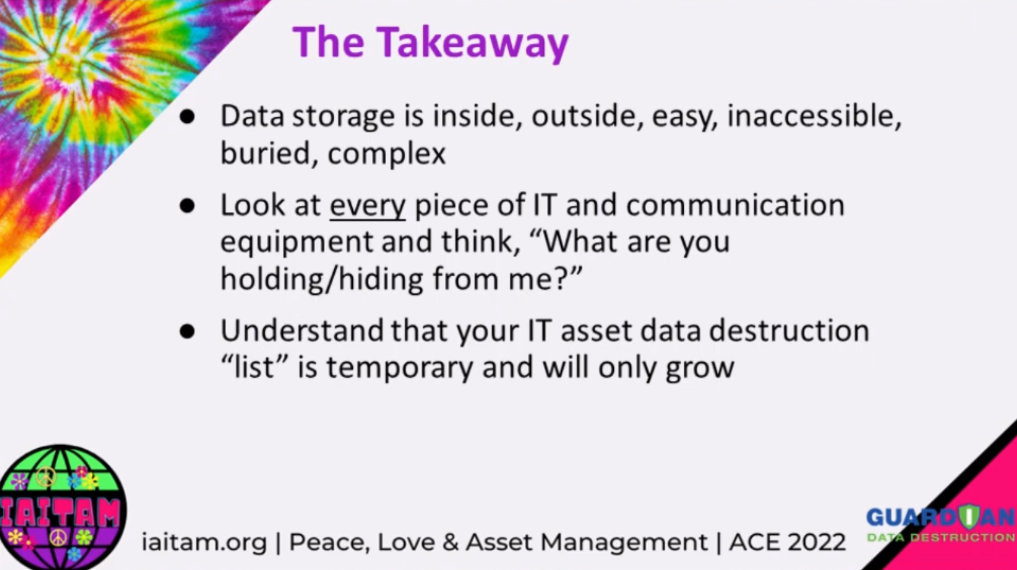
Data storage is inside, outside, easy, inaccessible, buried and complex.
Look at every piece of IT and communication equipment and think, “What are you holding/hiding from me?”
Understand that your IT asset data destruction “list” is temporary and will only grow.
Action Items for IT Risk Management
- Review your IT asset management plan annually to ensure that IT assets, devices and technologies are recognized, tracked, inventoried and sanitized
- Work with your legal experts, industry groups and vendors to know the laws, regulations and requirements that apply so you can develop processes to ensure privacy and data security
- Understand the value of your data to unauthorized users to evaluate the risk of a data breach and estimate possible brand and monetary damage
- Work with your VAR, ITAD, reseller or MSP to ensure that you have a NAID AAA Certified data destruction advisor and provider
- Ensure that data destruction is in your annual budget (instead of a
- Share this blog and accompanying recorded video from the IAITAM ACE 2022 Conference with your team to increase engagement in enterprise-wide data protection.
Additional Guardian resources for IT Risk Management
In addition to the above, review 30 common places your company data is stored (and waiting for a breach).
Take advice from 5 experts who contributed to our weeklong series about data privacy: John Shegerian of ERI, Melissa Graham of SHI International, Eric Ingebretsen of TES, Joe Marion of ASCDI, Christian Foster of CircleIT and Eric Dorn of Sipi Asset of Recovery.
No matter the industry or location, Guardian reduces risk, reduces cost and reduces overhead for our partners while shouldering the burden of compliance, industry and logistics. Review our data privacy by industry blog or view your industry regulations here.
Don’t leave a shred of data behind. Sign up to receive data destruction news.