A guide to Data Bearing Devices/Assets. Download your free copy here >
5 ways to make Data Privacy Week 2023 a security win
How to make the most out of Data Privacy Day 2023
Is January 28th highlighted on your calendar? If not, it’s time to add the international day of privacy and data protection awareness as a recurring calendar event.
Why? Data Privacy Day, every January 28th, is an annual nudge to look under the hood and do an oil check on your personal and corporate data privacy and security measures and efficacy.
“The Convention for the Protection of Individuals with Regard to Automatic Processing of Personal Data ” aka Convention 108 was formed by the Council of Europe in 1981. The first Data Privacy Day was celebrated in 2007. In 2008, the US and Canada joined the awareness campaign and in 2022, the National Cybersecurity Alliance encouraged all persons, agencies and companies to protect their data by observing Data Privacy Week.
This year, don’t let the Saturday-ness of Data Privacy Day trick you into putting off checking your data dipstick. Starting last year, Data Privacy Day is the culmination of Data Privacy Week which gives you a full five days to take action.
No excuses for not checking data privacy
We’ve put together five suggestions to tighten up your data privacy and data security and bolster your defense against a data breach. Just do just one of these suggestions each day of Data Privacy Week so that you can breathe easily when Saturday rolls around.
5 Days = 5 Ways to increase your data privacy for 2023
1) Refresh yourself with our expert recommendations from 2022. They are still relevant and applicable!

“… make it a priority to safeguard the data stored on electronic devices. Not enough organizations pay attention to the potential of a compromising breach via the electronics hardware they use … and what happens to that confidential information and its stored data at asset disposition.”
John Shegerian, Chairman/CEO
“The Data Privacy Week Wrap-up” >

“…Data Privacy Day is an opportunity for any company to step back, take a breath and see where their data resides in this increasingly hybrid environment.
- How can you create robustness and resiliency in data storage?
- How can you ensure that remote workers are following data security protocols?
- What do you do to destroy data on devices in the field before they are shipped and vulnerable to theft?
Melissa Graham, Senior Vice President, Global Sales
- How is your procurement department balancing risk and costs?“
“Why Should You Care about Data Privacy Day” >

“…ASCDI honors its members for respecting customer data and privacy in the reuse of IT and communications equipment processes. ASCDI membership requires strict adherence to our Code of Ethics and a commitment to protecting customer data and the environment through the ASCDI ITAD Certify program.”
Joe Marion, President
“Finding trusted vendors that align with your company asset management policies” >
“…when assessing vendors look for companies that offer secure IT asset services that serve your company goals and your employees’ personal needs – especially those of remote workers.”
Christian Foster, SVP
“Finding trusted vendors that align with your company asset management policies” >

“…we recommend evaluating your partners and downstream third-party provider vetting process. It should be robust enough to adhere to your company’s stringent policies and procedures covering compliance with government regulations, experience with industry standards, the highest level of certifications and untarnished financial and legal records.”
Eric Ingebretsen, Chief Commercial Officer
“What the Experts Want You to Know about” >

“…with a strict chain of custody process that is adhered to, you’ll significantly reduce the opportunity for an accidental or nefarious data breach and keep your brand reputation intact.”
Eric Dorn, Senior Vice President & General Manager
2) Review your current data destruction plan and process (or create one!)
- Has anything changed? New technology? New mandates? New concerns?
- What is your data security strategy for remote workers and satellite offices?
- Can you adopt a hybrid data destruction program (hard drive shred + hard drive erasure) that protects data while preserving hard drives?
3) Educate your workforce to create a culture of privacy and security.
If you’re patting yourself on the back because you’re the data privacy and security whiz, why not create a stakeholder army? After all, if they don’t understand the risk of data left on a laptop, a USB port or an old printer, the opportunity for data theft from sheer ignorance or sloppiness is far greater. In fact, IAITAM 2022 attendees emphasized that their biggest issue preventing a data breach through employee negligence or ignorance.
Suggestions:

- Host a training session
- Bring in an industry speaker
- Give a pop quiz (be sure to give out prizes for the know-it-alls)
- Review current policies with managers and get their input. And buy-in!
- Develop common sense internal processes materials for onboarding, ongoing training and turnover.
4) Ramp up your data center server hardware knowledge.
Data storage configurations are not standardized. And they’re frequently expanded or altered. These switches and upgrades are not always (read: rarely) documented which may result in serial # mismatch affecting data destruction’s chain of custody. If the storage has been replaced, expanded to full capacity or increased internally (back or inside) without any type of documentation, data may be unknowingly left on the device solely due to a field change that is not visible or recorded.
Our initial recommendation is to put a process in place that documents added or replaced data storage. For all server equipment that is scheduled for wiping, look beyond the standard hard drive that sits in front of you. We often find non-standard “surprises” like these:
- Hard drives located in multiple places on a single server – front/rear/legacy
- External hard drives + internal hard drives + one or more SSDs on the motherboard
- OS system on a MicroSD accessed through the controller
Review this Asset Checklist to Evaluate for IT Risk Management designed for Information technology departments including IT asset managers (ITAM) and IT security, procurement, engineers, legal teams, ITADS, office managers and facilities managers who know what equipment, machines and devices are in the office, the factory, the workforce and the home.
[Video] How IT Asset Managers can Prevent Data Breaches (a recorded IAITAM 2022 session) >
5) Audit digital devices for unknown data sharing and storage.
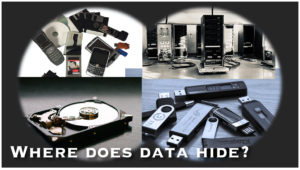
With the Internet of Things (IoT) connecting and sharing information, explore where your data may be unknowingly shared and stored. It’s not just the obvious laptops, desktops, networks, data centers and backup systems. It now includes smartphones, modems, cars, printers, copiers, point-of-sale (POS) devices, and more.
- What steps can you take to prevent synchronized devices from grabbing data that isn’t needed?
- Is that device also backing up the data into an unauthorized or unreachable server?
- Do you have smart devices holding data that you’re not even thinking of like copiers or printers that may have legal, proprietary or employee data stored as last printed or spooled documents?
See a full list of unexpected places your data may be stored >
Guardian is the last step in data protection

No surprise: every day is Data Privacy Day here. Data security is the very foundation of our services and approach.Whether it’s hard drive shredding, hard drive erasure, hard drive degaussing, secure IT packing, secure IT logistics, secure storage or secure warehousing, our focus is on secure, secure, secure.
In parallel to our suggestions above, The National Cybersecurity Alliance recommends these three steps to keep sensitive information secure:
- Conduct an assessment of your data collection practices – locally, nationally or globally. Determine if it is secure, processed in a fair manner and collected/saved for true need. Do not forget oversight and responsibility for partners and vendors as you are ultimately responsible.
- Adopt a privacy framework to manage risk throughout your organization. See NIST Privacy Framework, AICPA Privacy Management Framework, ISO/IEC 27701 – International Standard for Privacy Information Management.
- Create a company culture of privacy through education and reinforcement.
As the undertakers of IT equipment all over the US in thousands of companies, we see it all. Chasing, tracing, finding and destroying data has become exponentially more difficult and time-consuming as technology gets smaller and more data is exchanged through the cloud and expanded IoT capabilities.
That’s why Guardian is often the last step in finding data and destroying it. What’s far more effective for data security is a comprehensive approach. Every business, whether it’s SMB or Fortune 100, medical or financial, should adopt a systematic company-wide, top down, all-hands approach to data location, data storage, data sharing and data destruction.
Need help? Ask your ITAD or VAR for their recommendations. Or, give us a call. Guardian is always here to reduce your risk of a breach or legal non-compliance.
Helpful reading:
Data destruction by industry guide >
Atypical data destruction solutions >
Kick off your company and community initiative with a big, loud event! >